Maybe you have heard about credential stuffing. Most likely, you have at least heard of the attack. To demonstrate the attack, let’s take the case that happened at a Product Company, an upcoming small business based in New York. One Monday morning, the CEO, Mary, went to work as usual. However, upon login into her email, Mary was in for a rude shock. She was greeted by more than twenty emails indicating that unknown devices had logged in to almost all her accounts from unknown locations. Perplexed, Mary immediately contacted the IT head to receive the shocking news that an attack had leaked passwords of all the employee on a dark website.
So, what happened? Before Mary could get a concrete answer from IT, her computer screen flashed. Upon checking, Mary saw a notification that frightened her to death.
“We have encrypted your network and all data. Pay five bitcoins if you want to regain access. Meanwhile, you have 72hours, and we shall leak all your data to the dark web.”
Despite being unfamiliar with cyber breaches, Mary instantly knew her company had become the victim of a ransomware attack.
In 2021 alone, at least 1,500 small businesses encountered costly ransomware attacks.
The CEO was still reeling from the shock when the IT head came in to brief her. One of the new interns had exposed one of the sensitive databases on the internet unintentionally. Unfortunately, the exposed website contained email addresses and passwords for each employee in the budding company. Furthermore, the malicious internet actors who came across the database were novices. Therefore, unsure of what to do with the information, they decided to sell the database to a dark website for $5. That’s right. It only took $5 to put Product Company and all the 500 employees in an absolute nightmare. In some dark websites, malicious actors buy stolen emails and passwords for as low as $0.70.
Request a Live Demo
Want to enhance your cybersecurity operations?
Are you looking for your first cybersecurity expert?
Want to gain visibility for your exposed assets?
You can request a live demo by scheduling date and time on our available hours:
The Incident Escalates
While deliberating with the IT head the best response to the incident, Mary’s phone rang. It was the company’s head of sales and marketing reporting the ransomware incident. He informed the CEO that the department could not operate since it could not access any data or network resources.
Even larger corporations, such as Colonial Pipeline, have shut down critical operations for days due to ransomware attacks. At the same time, several employees reported that all accounts associated with their email addresses had been hacked. Product Company was yet to provide employees with corporate email addresses, and they were still using their Gmail accounts for work.
Every employee was affected, and the floodgates were still to open. Then, suddenly, one of the top company customers called demanding to know why his personal and business information had been found on the dark web. At this point, Mary started losing it. At the moment, the company was under a ransomware attack, and almost every employee and customer data had been leaked online.
However, with the time ticking, the CEO decided to contact the company’s cyber insurance firm. She was determined first to address the ransomware incident so the small company can resume business operations. But, certain that the insurance firm would pay the ransom, Mary was in for another rude shock. The company’s agreement with the insurance firm was that the insurer would cover any ransomware incidents.
Unfortunately, the agreement did not include a scenario where the insurer would chip in due to lax cybersecurity practices. Besides, with the insurance market being relatively new, there are no standardized policies of how insurers can determine or define an incident before covering it. In fact, one of the clauses in the Product Company’s coverage stated that the insurer would not be obligated to step in if the cause of a cyber incident was a lax cybersecurity practice. Investigations would later reveal that the ransomware attack was a result of a reckless database leak. Now, Mary faced an uphill task of bringing back all systems and data online all on her own. The thought of firing the responsible intern crossed her mind, but she decided to deal with that later.
The Resulting Consequences
The biggest impact of the incidence was the inability to conduct any business. A ransomware attack encrypts sensitive information and systems until the victim pays the demanded ransom. In some cases, a company can restore backups and restore essential assets to resume operations. However, in the case of the Product Company, it did not have a backup policy. Although the company operated a cloud account, no one bothered to make any backup. In any case, employees, including the CEO, thought they were too small to be a hacker’s target. Employees who created backups only did so when they remembered, which was not very often. Now, the chicken had come back to roost, leaving the company unable to operate.
Secondly, all employee and customer sensitive information had been compromised. The adversaries who bought the leaked passwords used the CEO’s credentials to log back to the network and exfiltrated every piece of data. Albeit being a small business, the company had global customers, including some residing within European Union countries. Therefore, the Product Company was subject to severe GDPR (General Data Protection Regulation) penalties. GDPR is a global regulation that protects EU citizens’ privacy anywhere in the world. As such, Product Company faced penalties exceeding four times its annual turnover.
The third consequence affected every employee and customer in the company. Through the leaked passwords, hackers had gained access to sensitive customer information. For example, every customer must provide an email address before engaging the company in any business. That said, hackers used the customer emails to attempt brute-force attacks on all accounts registered using the same email. In addition, some customers observed password security best practices and were, therefore, not victims of the brute force attacks.
Employees were not so lucky. The password leak revealed their emails and passwords. In many cases, individuals use the same password and email as login credentials for multiple accounts. As a result, the hackers simply used the same credentials to access and compromise every account associated with Product Company’s employees. Hence, this explains why Mary was shocked to find email notifications that unknown devices had access to her different accounts from multiple locations.

What could the Product Company have done to Avoid the Password Leak?
Upon further investigations, Product Company found that employees had not been trained for more than two years. In addition, the intern responsible for the leak had joined the company just two months before the incident. Therefore, the Product Company should have implemented robust employee training and awareness programs. An effective policy should require all employees to attend training programs every 4-6 months.
From the incident, it is clear that Product Company employees lacked basic cybersecurity skills. For example, the company should have stored all passwords in an encrypted database. That way, it would be impossible for anyone to access the passwords even if they were leaked. Besides, the incidence revealed that the employees use the same email and password to secure different accounts. Best password security practices dictate that everyone should use unique usernames and passwords to protect different accounts.
Additionally, the incidence showed that the Product Company was not compliant with essential regulations. For example, most current regulations require a company to implement strong access controls to prevent unauthorized access to confidential data. That said, it is still unclear why a new intern would have access to a sensitive database housing all employee emails and passwords. Besides, global regulations like the GDPR mandate companies to implement customer privacy protection measures. These include data encryption and data privacy by design. The attack showed that the Product Company had implemented neither. If it had complied with mandatory compliance requirements, the Product Company would not have suffered the password leak and resulting incidences.
Lessons Learned from the Incidence.
- Employee training is essential.
The essence of cybersecurity training and awareness is to equip users with the best security practices. For example, password security, a cornerstone of organizational cybersecurity, is critical. Training educates users on how to create and manage strong passwords. Moreover, it increases awareness of the importance of securing different accounts using unique usernames and passwords. Therefore, every small business has a responsibility to implement sufficient cybersecurity training and awareness programs.
- Information access controls Are necessary
Data is the primary driver for most business operations today. With data being such a critical asset, it is only sensible for a company to implement robust access control schemes. For example, role-based access control allows employees to access specific information based on their roles. Such a policy would have prevented the intern from accessing the sensitive database. Other access control measures include least-privilege access control. The mechanism only provides access to information needed to complete a specific task.
- Password leakage can cause more dangerous incidents
As this story shows, the password leak incidence caused a ransomware attack. Most likely, the attack would not have occurred if the intern had not leaked the database unintentionally. Ransomware attacks are severe since it is a form of extortion. Also, paying the ransom does not guarantee that a company will recover all its data. Additionally, leaked passwords can provide unauthorized access, which may cause unwanted impacts. For instance, malicious competitors can use leaked credentials to access a company’s intellectual properties or competitive strategies. Some can go a step further to put the affected company out of business by stealing their customers and business ideas. Therefore, it is critical for business owners to prevent password leakage at all costs.

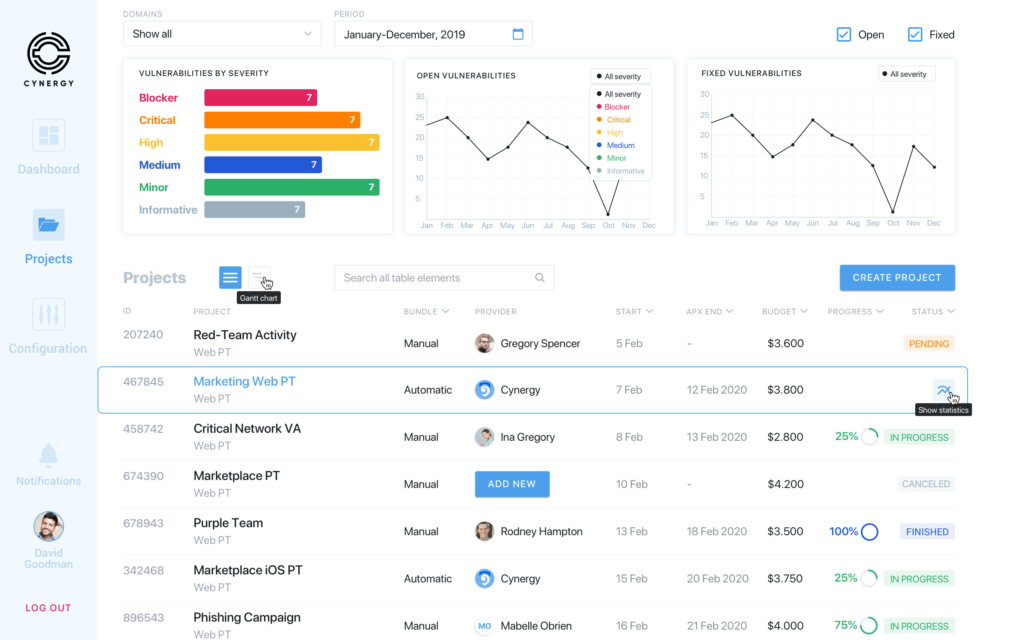
Protect Your Business from Data Leakage
Cynergy enables your company to achieve company visibility of your company’s data flows. Specifically, Cynergy offers a risk-driven, asset discovery platform. With the platform, you can identify all digital assets continuously. These include infrastructure, cloud, mobile, and web assets. In addition to asset identification, Cynergy provides a reliable platform that identifies employee or customer data leakage. For example, you can detect sensitive information leaked to various sites. Timely identification of data leakage enables rapid action to counter resulting risks. More importantly, you get to conduct dedicated awareness campaigns to prevent similar incidents in future.